A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised Linux hosts.
“This particular campaign involves the use of a number of novel system weakening techniques against the data store itself,” Cado security researcher Matt Muir said in a technical report.
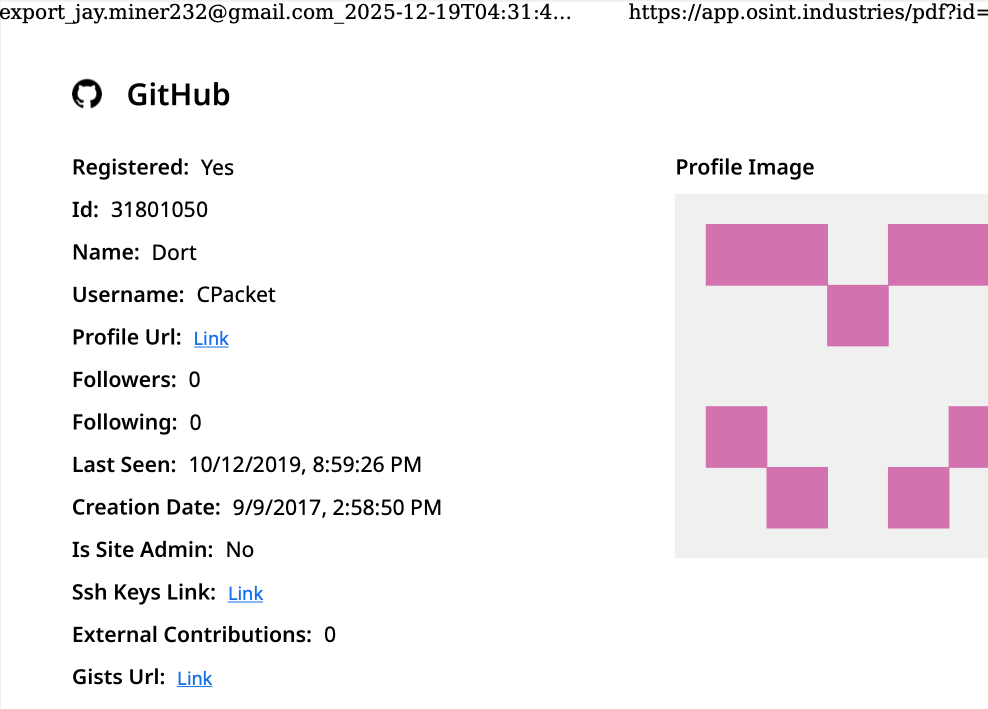
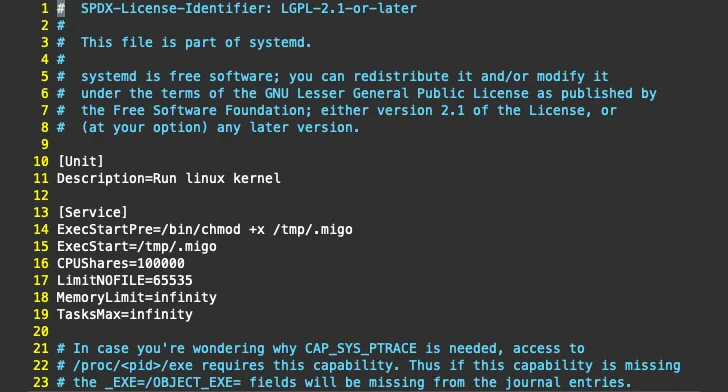
The cryptojacking attack is facilitated by a malware codenamed Migo, a Golang ELF binary that comes fitted with compile-time obfuscation and the ability to persist on Linux machines.
The cloud security company said it detected the campaign after it identified an “unusual series of commands” targeting its Redis honeypots that are engineered to lower security defenses by disabling the following configuration options –
It’s suspected that these options are turned off in order to send additional commands to the Redis server from external networks and facilitate future exploitation without attracting much attention.
This step is then followed by threat actors setting up two Redis keys, one pointing to an attacker-controlled SSH key and the other to a cron job that retrieves the malicious primary payload from a file transfer service named Transfer.sh, a technique previously spotted in early 2023.
The shell script to fetch Migo using Transfer.sh is embedded within a Pastebin file that’s, in turn, obtained using a curl or wget command.
 |
| Persistence |
The Go-based ELF binary, besides incorporating mechanisms to resist reverse engineering, acts as a downloader for an XMRig installer hosted on GitHub. It’s also responsible for performing a series of steps to establish persistence, terminate competing miners, and launch the miner.
On top of that, Migo disables Security-Enhanced Linux (SELinux) and searches for uninstallation scripts for monitoring agents bundled in compute instances from cloud providers such as Qcloud and Alibaba Cloud. It further deploys a modified version (“libsystemd.so”) of a popular user-mode rootkit named libprocesshider to hide processes and on-disk artifacts.
It’s worth pointing out that these actions overlap with tactics adopted by known cryptojacking groups like TeamTNT, WatchDog, Rocke, and threat actors associated with the SkidMap malware.
“Interestingly, Migo appears to recursively iterate through files and directories under /etc,” Muir noted. “The malware will simply read files in these locations and not do anything with the contents.”
“One theory is this could be a (weak) attempt to confuse sandbox and dynamic analysis solutions by performing a large number of benign actions, resulting in a non-malicious classification.”
Another hypothesis is that the malware is looking for an artifact that’s specific to a target environment, although Cado said it found no evidence to support this line of reasoning.
“Migo demonstrates that cloud-focused attackers are continuing to refine their techniques and improve their ability to exploit web-facing services,” Muir said.
“Although libprocesshider is frequently used by cryptojacking campaigns, this particular variant includes the ability to hide on-disk artifacts in addition to the malicious processes themselves.”