Malicious Google Security Checkup That All Gmail Users Need To Know About
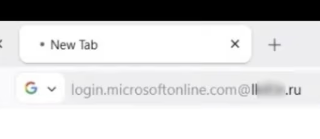
“Disguised as a routine security checkup,” Malwarebytes researcher Stefan Dasic confirmed in a that the attack “walks victims through a four-step flow that grants the attacker push notification access, the device’s contact list, real-time GPS location, and clipboard contents—all without installing a traditional app.”Not surprisingly, then, Malwarebytes has described this “cleverly [...]